How to remove a Rootkit Virus

I couldn’t use the removal tool that I normally use because it isn’t compatible with Windows 8, so I did some research and found a different tool called GMER.
What is a Rootkit Virus?
But before I go on and explain how useful the tool was, I’ll just quickly explain what a Rootkit Virus is.
The name comes from a term used in Unix and Linux Operating Systems, with “Root” referring to a “Privileged” account or in other words an account with Administrative rights, whilst the “kit” part of the name refers to software components that implement it. A Rootkit virus assumes admin control of the Operating System, making it very difficult to remove.
So having found that my usual bag of tricks was not going to work, it was time to find something else.
During my research, I came across a removal tool that I hadn’t heard of before (as previously mentioned, GMER), and I gave it a shot.
To my surprise it was very simple and effective.
I downloaded the Removal Tool, and unlike many other tools, I didn’t have to rename the executable file to something that a potential virus wouldn’t recognise and therefore prevent running, because it is already named with a random file name at download. It was also a very small file size of 372kb.
GMER scans for the following:
- hidden processes
- hidden threads
- hidden modules
- hidden services
- hidden files
- hidden disk sectors (MBR)
- hidden Alternate Data Streams
- hidden registry keys
- drivers hooking SSDT
- drivers hooking IDT
- drivers hooking IRP calls
- inline hooks
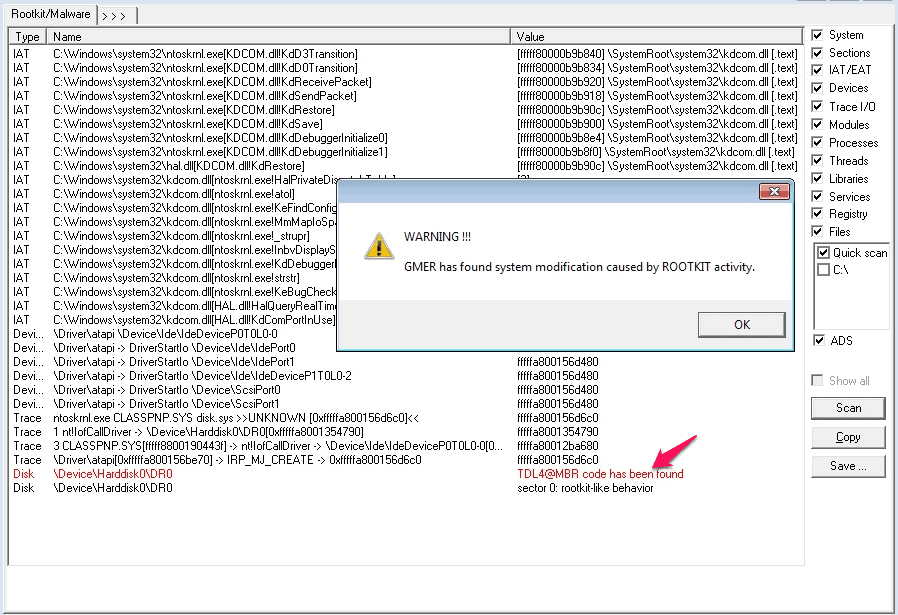
If a Rootkit Virus is present, you will be notified with a screen that looks like the following:
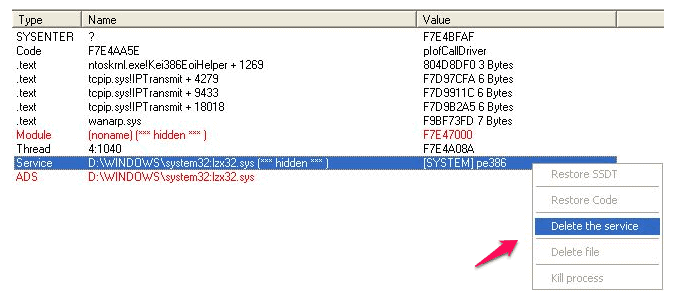
Removing the identified viruses involves right clicking on the identified virus and choosing “Delete the Service”.
Spotty Dog Computer Services can remove Root Kit Viruses from your PC.